Frequently asked questions
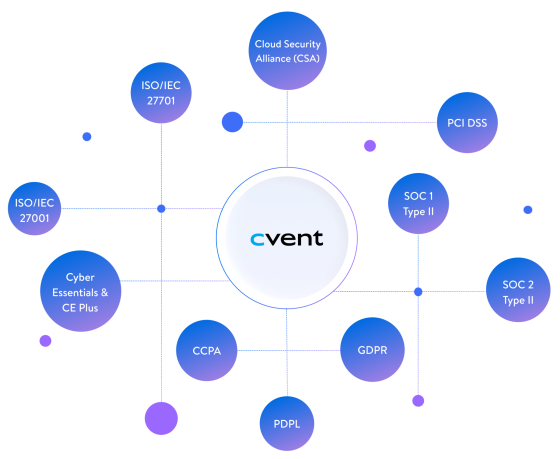
Yes. Cvent has a comprehensive Information Security Policy and maintains over 30+ different policies and procedures covering multiple areas such as Security Awareness & Training, Encryption Management, Disaster Recovery, Business Continuity, Change Management, Password Policy, Security Logging and more. All policies and procedures can be found on our Trust Center.
Yes. Cvent encrypts all customer data in-transit via TLS v1.2 encryption and at-rest via AES-256 encryption. In addition, Cvent offers field-level encryption for any field designed to contain potentially sensitive information, such as Date of Birth, Social Security Number, Passport ID, and more.
Yes. Cvent maintains both programs to ensure that customer data is secured and available in the event of any type of disaster that may occur or to allow Cvent to quickly recover in the event of unexpected downtime. Both policies are available for review on our Trust Center.
Cvent utilizes AWS for all customer data storage needs. Data will be processed/stored within AWS US-East and AWS US-West for all North American-based customers, and AWS Frankfurt and AWS Dublin for all EU-based customers and customers in other parts of the world.
Yes. Cvent will notify customers who are directly impacted by a security breach/incident within 48 hours of confirmation.
Yes. Cvent performs internal testing on all of our products/services and also works with independent third-party vendors to perform additional testing. The results of this testing are shared with us as an Executive Summary report, which can be shared with our customers upon request.
Yes. The majority of our products will support SSO out of the box and additionally we offer APIs that can be configured to work with your preferred solution. Please visit out Developer Portal for more information on our SSO offerings.
Yes. Cvent completes detailed security assessments and reviews them annually to ensure they are current. Examples of assessments that we offer are a Standardized Information Gathering (SIG), the Consensus Assessments Initiative Questionnaire (CAIQ), architecture and data flow diagrams, and more. All of this information can be found on our Trust Center.